laptop wifi card monitor mode

Title: Panda PAU09 WiFi Adapter Kali Linux Monitor Mode
Channel: Divine Zeal
Panda PAU09 WiFi Adapter Kali Linux Monitor Mode by Divine Zeal
laptop wifi card monitor mode, does my wifi card support monitor mode, how to put wifi card in monitor mode windows 10, what is wifi monitor mode
Laptop WiFi Card: Unlock Hidden Network Secrets (Monitor Mode!)
Unveiling the Secrets Within: Your Laptop's WiFi Card as a Network Super Spy
So, you have a laptop. You connect it to WiFi. That's the gist of it, right? But what if I told you your laptop's WiFi card held a secret? A power beyond simple browsing. It could be your entry into the hidden world of network analysis. Intrigued? Let's dive in.
Beyond Browsing: The Realm of Monitor Mode
Most of us use our WiFi cards for everyday tasks. We check emails, stream videos, and scroll through social media. These applications utilize the basic "station" mode. However, your WiFi card is far more versatile than you realize. It’s capable of something called "monitor mode."
Monitor mode unlocks a whole new level of network insight. Instead of just passively receiving data, your card becomes a listener. Think of it as eavesdropping, but in a perfectly legal and ethical way (usually!). It lets you see all the WiFi traffic around you. This is regardless of where it's headed or who it's coming from.
Unveiling the Data Stream: What Can You Actually See?
Now, you are probably asking, "Okay, so what can I see?" That's a great question! Monitor mode provides a wealth of information. It allows you to:
- Observe Wireless Networks: See all the available networks, even hidden ones.
- Capture Packets: Sniff out the raw data packets. This is great for analysis.
- Analyze Network Traffic: Understand the flow of data on a network.
- Identify Devices: Pinpoint connected devices and their MAC addresses.
- Troubleshoot Issues: Diagnose network problems quickly and accurately.
- Enhance Security: Identify potential vulnerabilities within a network.
Essentially, it grants you a comprehensive view of the wireless landscape. Moreover, this is crucial for anyone interested in network security, penetration testing, or even just wanting to learn more about how WiFi works.
The Ethical Tightrope: Use Responsibly
Before we proceed any further, let's talk about ethics. As you can see, monitor mode provides considerable power. As a result, it's crucial to use this power responsibly. Never use monitor mode to capture sensitive data or to snoop on networks without explicit permission. Always respect privacy. Always adhere to all applicable laws and regulations. Because the misuse of these tools can have serious consequences. Your actions should always be ethical and lawful.
Setting Up Your WiFi Card for Adventure
Getting your WiFi card into monitor mode is a bit like training a puppy. It takes patience and practice! The exact process depends on your operating system and WiFi card model. Generally, you'll need the following:
- A Compatible Card: Not all WiFi cards support monitor mode. You might need to research your card's capabilities.
- The Right Tools: You will need network analysis software. Popular options include Wireshark and Aircrack-ng.
- Basic Command-Line Knowledge: Navigating a terminal is essential. You'll need to issue commands to configure your card.
For example, let's illustrate some simple steps. With a Linux system, you'd likely use the "airmon-ng" tool. This tool helps with putting your card into monitor mode. The basic steps would typically look like this:
- Identify Your Interface: Use commands like
ifconfigoriwconfigto find your wireless interface (usually something likewlan0orwlp2s0). - Stop Network Manager: Disable the network manager to prevent interference.
- Enable Monitor Mode: Run a command similar to
airmon-ng start wlan0. - Start Capturing Packets: Launch a packet capture tool like Wireshark.
- Analyze the Results: Examine the data.
Diving Deep: Packet Analysis and Beyond
Once your card is in monitor mode, the real fun begins. Launch a program like Wireshark. Start capturing packets. You'll see a flood of data. It will look like a jumble of information at first. Don't let that scare you! With a little practice, you'll start to understand what you are seeing.
You can filter the packets. That allows you to focus on specific types of traffic. You can also decode the packets. This way you can see the underlying data in human-readable form. Consider examining the various network protocols. This can include HTTP, TCP, UDP, and many others.
Advanced Techniques: Beyond Basic Packet Sniffing
Monitor mode opens doors to advanced techniques. You can perform:
- Wireless Network Auditing: Penetrate your own network to test for vulnerabilities.
- Wireless Intrusion Detection: Monitor for suspicious activity.
- Deauthentication Attacks: Kick devices off a network. (Use this with extreme caution and only with permission.)
- Packet Injection: Craft and send your packets to the network.
These techniques require more advanced knowledge. You must also demonstrate respect for the law. It's important to use these skills responsibly.
Final Thoughts: Embrace the Power, Respect the Responsibility
Your laptop's WiFi card is not just a way to connect to the internet. It’s a gateway to a deeper understanding of networking. With monitor mode, you can explore the inner workings of WiFi. You can increase your knowledge and skills.
Remember, with great power comes great responsibility. Use this knowledge ethically. Always respect the privacy of others. Go forth, explore the wireless world. But always stay within legal and ethical boundaries. This technology grants you insight. Harness this power wisely and responsibly. Happy exploring!
Dell WiFi Nightmare? Solved! (Easy On/Off Guide)Laptop WiFi Card: Unlock Hidden Network Secrets (Monitor Mode!)
Hey tech enthusiasts, code whisperers, and network ninjas! Ever felt like your laptop's Wi-Fi card was a locked door to a world of network secrets? Well, guess what? You're right! And today, we're grabbing the key to unlock it, specifically with something called "Monitor Mode." Think of it like having Superman's X-ray vision for Wi-Fi signals. Ready to dive in? Let's go!
1. The Mysterious World of Wi-Fi Cards: Beyond the Web
We all use our Wi-Fi cards daily, right? Checking emails, streaming videos, posting cat pictures (guilty!). But how much do we really know about these tiny, indispensable components? Most of us see them as a magical portal to the internet, a seamless link. But they're so much more. They're intricate pieces of hardware capable of sending and receiving radio waves, interpreting data, and connecting us to the digital world. It's like an unsung hero working silently in the background, tirelessly doing its job.
2. What Exactly Does a Wi-Fi Card Do, Anyway?
At its core, a Wi-Fi card translates digital data into radio waves (and vice versa). It communicates with your router, which in turn communicates with the internet. It handles everything from security protocols to signal strength, constantly adapting to the ever-changing network environment. It's a complex dance of signals and data packets, all working in perfect harmony. Think of it as the conductor of an orchestra, orchestrating the flow of information.
3. The Normal Operation: A Closed-Off View
Usually, your Wi-Fi card operates in what's called "managed mode" or "infrastructure mode." In this state, it's like having tunnel vision. The card only sees and interacts with data packets specifically addressed to your device or broadcast by your router. It filters out everything else, focusing solely on what's deemed relevant for your internet connection. It's efficient, but it also limits your perspective.
4. Introducing Monitor Mode: The Open-Source Lens
Now, here's where things get interesting. Monitor Mode, also sometimes called "promiscuous mode," turns your Wi-Fi card into a network detective. It allows your card to passively listen to all wireless traffic in its range, not just the packets addressed to it. It's like switching from tunnel vision to panoramic vision. You can see all the data flying through the air, including everything from network handshakes to password attempts (more on the ethical implications later!).
5. Why Bother with Monitor Mode? Unveiling Hidden Possibilities
So, why should you care about Monitor Mode? Well, it opens up a whole new world of possibilities:
- Network Analysis: Diagnose network problems, identify bottlenecks, and understand how your network is behaving. Is your signal dropping out? Is someone hogging all the bandwidth? Monitor Mode can help you find out.
- Security Auditing: Test the security of your own network. Identify vulnerabilities, and ensure your passwords are secure. It's like having a security guard for your digital house.
- Wireless Packet Sniffing: Capture and analyze wireless traffic. This is where you can see the raw data packets, revealing fascinating insights into network communication. Think of it like being able to "see" the whispers of data.
- Wireless Intrusion Detection/Prevention: Identify possible wireless intrusions and block malicious traffic that uses your network as a means to connect to the Internet.
6. Setting the Stage: Hardware and Software Prerequisites
Before we jump in, let's talk about what you'll need:
- A Laptop with a Wi-Fi Card: Most modern laptops have Wi-Fi cards, but check that it supports monitor mode. Many do, but some older or less feature-rich cards might not. Research your card beforehand.
- Operating System: Linux is the preferred operating system for Monitor Mode due to its extensive support for wireless networking tools (more on this later).
- Software: You'll need tools like
airmon-ng(part of theaircrack-ngsuite),tcpdump, andWireshark. These are your detective tools.
7. Diving into Linux: The Gateway to Wireless Power
Why Linux? Because it gives you far more control over your hardware and provides a rich ecosystem of networking tools. Think of Linux as the ultimate toolbox for network analysis. It’s like giving a master craftsman a set of perfectly calibrated tools.
8. Enabling Monitor Mode: The Technical Breakdown
The process of putting your Wi-Fi card into Monitor Mode usually involves these steps:
- Identify your wireless interface: Use the
iwconfigorifconfigcommand to find the name of your Wi-Fi card's interface (e.g.,wlan0,wlp2s0). - Bring the interface down: Use the
ifconfig <interface> downcommand. Think of it as putting your Wi-Fi card to sleep. - Enable Monitor Mode: Use the
airmon-ng start <interface>command. This is the magic spell! - Verify Monitor Mode: Use
iwconfigagain. You should see the interface name has changed (e.g.,wlan0mon), and it should be in monitor mode.
9. Sniffing the Airwaves: Capturing Wireless Traffic
Once your Wi-Fi card is in Monitor Mode, you can start capturing wireless traffic.
- Using
tcpdump: A powerful command-line tool for capturing network packets. You can filter packets based on various criteria (e.g., source/destination IP addresses, protocols). It’s like using a powerful telescope to scan the skies of your network. - Using Wireshark: A graphical packet analyzer. It allows you to view and analyze captured packets in a user-friendly interface. It’s like having a microscope for your network traffic.
10. Decrypting WEP/WPA/WPA2: Unraveling Encrypted Secrets
- The Ethical Considerations: Before you even think about decrypting any wireless network's password, you must have permission to do so, as doing so is illegal without the proper authorization.
- The Tools: Tools such as
aircrack-ng, are most commonly used to attempt to crack the passwords of WEP, WPA, and WPA2 encrypted networks. - Process: Capturing the WPA/WPA2 handshake with
tcpdumporWireshark. Using aircrack-ng to attempt to crack the captured handshake by trying out passwords and looking up possible passwords in a dictionary.
11. Ethical Considerations: Tread Carefully!
Monitor Mode is powerful, but it's also a tool that can be used for malicious purposes. Always remember to play by the rules:
- Obtain Permission: Never monitor or analyze a network without explicit permission from the network owner. This is crucial!
- Respect Privacy: Be mindful of the sensitive information you may encounter. Avoid capturing or storing personal data unless absolutely necessary and with proper consent.
- Use for Good: Focus on using Monitor Mode for legitimate purposes, such as network security research, troubleshooting, and educational purposes.
12. Practical Examples: Real-World Applications
Let's look at a few practical examples:
- Identifying Rogue Access Points: Monitor Mode can help you detect unauthorized Wi-Fi access points that may be compromising your network security.
- Troubleshooting Wi-Fi Issues: Analyze packet loss, signal strength, and other metrics to pinpoint the cause of network problems.
- Creating a Wireless Intrusion Detection System (WIDS): Build a system that automatically detects and alerts you to suspicious network activity.
13. Advanced Techniques: Going Beyond the Basics
Once you're comfortable with the basics, you can explore more advanced techniques:
- Wireless Injection: Injecting packets into the network to test security vulnerabilities.
- Deauthentication Attacks: Disconnecting devices from a Wi-Fi network (for testing purposes).
- Custom Scripting: Automating complex network analysis tasks.
14. The Future of Wireless: Stay Curious and Keep Learning
The world of wireless networking is constantly evolving. New technologies, security protocols, and attack vectors emerge all the time. Here's what to do to stay ahead of the curve:
- Follow the Experts: Read blogs, attend webinars, and follow cybersecurity professionals.
- Practice Regularly: Hands-on experience is key. Set up your own test network and experiment with different tools and techniques.
- Contribute to the Community: Share your knowledge, participate in forums, and help others learn.
15. Final Thoughts: Unleash Your Inner Network Alchemist
Monitor Mode is a powerful tool that can transform your understanding of wireless networking. It’s like being able to see the hidden patterns and interactions that govern the digital world around us. Remember to use it responsibly, ethically, and always with the proper authorization, and always treat it as a starting point and a tool to hone your skills and knowledge of wireless networks.
Closing Segment
So, there you have it! We've explored the ins and outs of your laptop's Wi-Fi card and learned how to unlock its hidden potential using Monitor Mode. Remember, this is just the tip of the
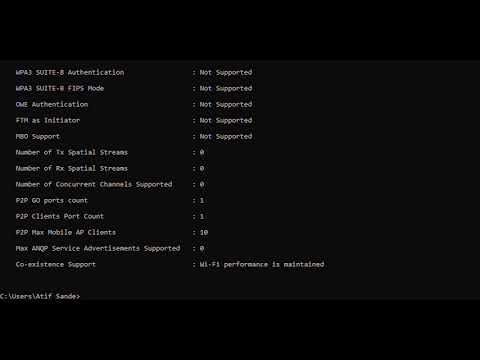
WiFi Nightmare on Windows 8? Fix Your Laptop's Network NOW!How To Check Inbuild Wi-Fi Card Supports Monitor Mode With cmd In Windows 10
By EtHaRay How To Check Inbuild Wi-Fi Card Supports Monitor Mode With cmd In Windows 10 by EtHaRay
Alfa adaptor which supports monitor mode and packet injection hacker wifi wifihacking

By HACKER SOCIETY Alfa adaptor which supports monitor mode and packet injection hacker wifi wifihacking by HACKER SOCIETY
Perbedaan Wifi Card Monitor Mode dan Standar Mode di Laptop

By TeknoXpert Perbedaan Wifi Card Monitor Mode dan Standar Mode di Laptop by TeknoXpert

Title: Best WiFi Hacking Adapters in 2021 Kali Linux Parrot OS
Channel: David Bombal
Best WiFi Hacking Adapters in 2021 Kali Linux Parrot OS by David Bombal
My Laptop Work
Laptop WiFi Card: Unlock Hidden Network Secrets (Monitor Mode!)
Have you ever felt like there’s a secret world of Wi-Fi activity happening around you, a realm unseen by your everyday browsing? A world where packets of data whisper secrets, and network interactions unfold invisibly? Well, you’re not wrong. And the key to unlocking this hidden world lies within your laptop's Wi-Fi card – specifically, its potential to operate in monitor mode. Prepare to transform your understanding of wireless networks, because we're about to embark on a journey into the fascinating capabilities of your laptop's wireless adapter.
Understanding the Fundamentals: Your Laptop's Wireless Card and Its Purpose
Let’s begin with the absolute basics. Your laptop's Wi-Fi card, also known as a wireless network adapter, is your gateway to the internet, allowing you to connect to wireless networks and communicate with the world. Think of it as a radio receiver and transmitter, constantly exchanging information with access points (APs) and other devices. Typically, your Wi-Fi card functions in "managed mode," the default setting that allows you to connect to and interact with a known wireless network. This is how you browse websites, stream videos, and send emails. But within this seemingly simple piece of hardware lies a hidden potential, a capability that allows it to go far beyond mere internet access – monitor mode.
What is Monitor Mode? The Key to Unveiling Wireless Activity
Monitor mode is an operating mode that allows your Wi-Fi card to passively listen to all wireless traffic on a specific channel. Instead of actively participating in a network connection (like in managed mode), your adapter becomes a silent observer. It captures every packet of data, regardless of its destination or source, giving you a comprehensive view of the wireless environment. This is akin to having a sophisticated listening device for the airwaves. It hears everything.
In essence, when your Wi-Fi card is in monitor mode, it’s no longer concerned with filtering out irrelevant data. It’s designed to record everything it encounters. This unfiltered access to wireless traffic opens up a whole new dimension of possibilities, from analyzing network behavior to identifying security vulnerabilities.
The Capabilities of Monitor Mode: More Than Just Passive Observation
The power of monitor mode extends far beyond mere passive observation. While simply “listening” is a core function, the gathered data is a treasure trove of information. Let’s delve into some key applications:
- Packet Analysis and Network Troubleshooting: By capturing and analyzing network packets, you can identify bottlenecks, diagnose connectivity issues, and troubleshoot performance problems. Imagine seeing the actual flow of data and pinpointing where delays occur.
- Wireless Network Auditing: This allows you to examine the security posture of wireless networks. You can assess the encryption protocols being used, identify weak passwords, and detect unauthorized access attempts.
- Wireless Intrusion Detection: Monitor mode enables you to detect suspicious activities, such as rogue access points or attempts to exploit vulnerabilities. You can set up alerts to notify you of potential security threats.
- Network Packet Capture (Sniffing): Sniffing is a powerful technique used to capture network traffic. This allows you to examine the inner workings of network communications, analyze application protocols (like HTTP or DNS), and understand how data is transmitted.
- Traffic Analysis: This is invaluable for understanding network behavior, identifying bandwidth consumption patterns, and detecting anomalous activities.
- Wireless Protocol Analysis: You can study protocols such as Wi-Fi Protected Access (WPA) and WPA2 and analyze what data is exchanged.
Enabling Monitor Mode: A Step-by-Step Guide
Enabling monitor mode isn’t necessarily complicated, but the process depends on your operating system and the specific Wi-Fi card you're using. Here's a general overview of the process, along with some specific considerations.
1. Identify Your Wireless Adapter and its Driver:
The first step is to determine the brand and model of your wireless adapter, and to ensure that you have the correct drivers installed. In most cases, your operating system will have the information. You can usually find this information in the Device Manager (Windows) or System Information (macOS and Linux).
2. Utilize Command-Line Tools (Linux):
Linux users will be happy to know that a command-line interface with pre-installed tools is usually the preferred method for enabling monitor mode. The most common tool is iwconfig (for older wireless drivers) and iw (for newer ones).
- Example using
iwconfig:- First, determine your wireless interface name (e.g., wlan0). You can usually find this information with the command
iwconfig. - To put the interface in monitor mode, use the command:
sudo iwconfig wlan0 mode monitor
- First, determine your wireless interface name (e.g., wlan0). You can usually find this information with the command
- Example using
iw:- First, get a list of wireless interfaces using
iw list. - Then, determine your interface.
- To put the interface in monitor mode, use the command:
sudo iw phy phy0 interface add mon0 type monitorwhere phy0 is the PHY number for your interface.
- First, get a list of wireless interfaces using
3. Leverage Third-Party Applications (Windows & macOS):
For Windows and macOS, specialized software tools are often used to enable monitor mode. Some popular options include:
- Wireshark: This is the most widely used network protocol analyzer in the world. While it doesn't directly enable monitor mode, it can detect if your adapter is in monitor mode and capture wireless traffic.
- Aircrack-ng Suite: A powerful suite of tools geared towards wireless security. AirCrack-ng is a good option to enable monitor mode.
4. Test Your Monitor Mode Configuration:
After enabling monitor mode, you need to verify that it's working correctly. The best way to do this is to use a packet capture tool.
- Wireshark: Open Wireshark and select your wireless interface. If monitor mode is enabled, you should see a stream of packets, even if you're not actively connected to a network.
tcpdump(Linux): This is a command-line packet analyzer. Runsudo tcpdump -i wlan0 -p -s 65535 -w capture.pcap(replace wlan0 with your interface name) to capture wireless traffic and save it to a file.
Ethical Considerations: Responsibility and Wireless Monitoring
While monitor mode is a powerful tool, it's essential to use it responsibly and ethically. Always obtain permission before monitoring a wireless network that you do not own or have authorization to access. Unauthorized monitoring can violate privacy laws and result in severe consequences. Moreover, be mindful of the data you're capturing and how you're using it.
Advanced Techniques and Further Exploration
Once you’ve mastered the basics of monitor mode, you can dive into more advanced techniques:
- Channel Hopping: Some tools can hop between different wireless channels to capture traffic on multiple channels. This dramatically increases your ability to see wireless activity.
- Packet Injection: Certain situations allow you to inject your own packets into a wireless network to test for vulnerabilities.
- Deauthentication Attacks (Ethical Use): These attacks can disconnect clients from a wireless network to analyze the security protocols.
- Wireless Security Analysis and Auditing: Armed with the data collected, you can use advanced tools to analyze wireless passwords and security vulnerabilities.
Conclusion: Your Gateway to the Wireless World
Monitor mode opens the door to a deep understanding of wireless networks. It's an invaluable tool for network administrators, security professionals, and anyone curious about the inner workings of wireless communication. As you delve deeper into the world of wireless data, you'll gain new perspectives on how networks function and become more aware of potential security threats. Embrace the power of monitor mode, explore the hidden depths of the wireless world, and unlock a new realm of knowledge.
