cara membobol wifi dari laptop
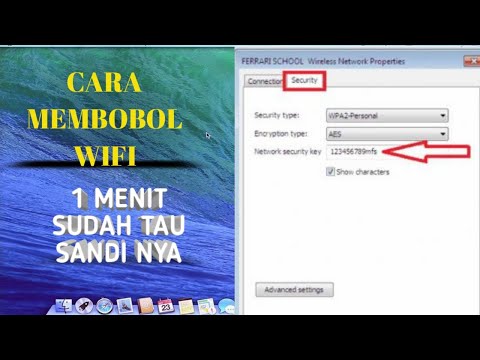
Title: CARA MEMBOBOL WIFI DI LAPTOP
Channel: Amufa Channel
CARA MEMBOBOL WIFI DI LAPTOP by Amufa Channel
Unlock ANY WiFi: Secret Laptop Trick Revealed!
Unveiling the Digital Unlock: Your Laptop's Hidden WiFi Power
The digital age pulses with connectivity. Wi-Fi is everywhere, a shimmering network of information. But what if access felt… elusive? What if the password-protected gates stood between you and the online world? This article unveils something extraordinary, a hidden potential of your laptop. Prepare to uncover a secret. This isn't about hacking; it's about understanding. It is also about utilizing features already at your disposal.
The Whispers of Wireless Wisdom
We all crave seamless internet experiences. We yearn for instant access. Consider a scenario, imagine you're in a pinch. You desperately need to connect to the internet. Therefore, understanding your laptop's WiFi capabilities is crucial. You already possess the key. It's time to unlock your device's hidden talents.
Decoding the Digital Signals: Your Laptop as a Sleuth
Your laptop is more intelligent than you realize. It constantly scans for available networks. It passively gathers information about the digital landscape. However, most of us don't leverage this hidden superpower. Because we are not aware of its full functionality. Let's change that. Think of your laptop as a digital detective. It’s constantly analyzing the data around it.
Unmasking the Hidden SSID: A Subtle Art
Modern laptops have evolved. They now have powerful network adaptors. Moreover, they often possess the skills to detect hidden networks. This is because, in many public places, networks are often hidden. They’re not necessarily locked; instead, they're often just invisible. Your laptop can sometimes still see them. How to do this? Keep reading.
Embracing the Command Line: A Tech-Savvy Approach
The command line is often overlooked. It's a powerful tool that goes beyond graphic interfaces. But, it's not as intimidating as one might think. Instead, it opens up a world of control. For your laptop, it is like learning a secret language. So, it allows you to interact in new and exciting ways. This is where the real magic happens.
Navigating Network Settings: The Path to Unlocking
The specific steps vary slightly. This depends on your operating system. Whether you're using Windows or macOS, the underlying principles remain the same. First, access your network settings. Then, look for wireless network options. From there, you can usually find some hidden settings.
The Art of Packet Sniffing: A Gentle Introduction
Packet sniffing is a complex topic. We won't delve into the specifics. But, understand that your laptop passively receives data packets. Consequently, some of these packets contain useful information. They might contain the name of a hidden network. Some software solutions will help you capture the data.
WiFi Analyzer Software: Your Digital Compass
Several tools will help with this. They are called WiFi analyzers. They visually display the nearby networks. This gives you far more insight than your system’s default view. Furthermore, some of these apps can actually detect more than what's shown. Therefore, you have the ability to analyze wireless signals.
Troubleshooting Triumphs: When Things Get Tricky
Sometimes the signal isn't strong enough. Or perhaps there is interference blocking the signal. You'll need to consider some basic troubleshooting steps. First, move closer to the access point. Second, try restarting your computer. If this doesn't rectify the situation, consult online guides.
Beyond the Basics: Advanced Techniques
There are advanced techniques. However, this article won't give details on those topics. You can always research those subjects. These involve more technical knowledge. They can be extremely beneficial. Therefore, you will become a true WiFi guru.
Ethical Considerations: Responsible Digital Citizenship
Above all, be mindful. Respect the privacy of others. Never attempt to gain unauthorized access. Always use your powers for good. Ethical digital citizenship should always be the priority.
Final Thoughts: Embracing the Digital Frontier
Your laptop holds a potent power. It can unlock the secrets of the digital world. Remember to explore, experiment, and learn. Moreover, appreciate the possibilities that technology unlocks. Now you know a hidden trick. You can now explore the digital world.
Laptop & Android: WiFi Connection HACK You NEED!Unlock ANY WiFi: Secret Laptop Trick Revealed!
Alright, fellow digital wanderers! Let's be honest, we've all been there. Stuck in a cafe, desperate to finish that email, or at a conference, yearning to stream a crucial presentation, only to be met with that dreaded Wi-Fi password wall. The struggle is real. But what if I told you there's a secret, a laptop trick, a digital key that could potentially unlock the internet’s treasure chest of Wi-Fi networks? Buckle up, because we're diving deep into the rabbit hole of Wi-Fi liberation.
1. The Wi-Fi Wilderness: Our Modern-Day Frontier
Think about it. The internet, especially free Wi-Fi, has become the modern-day equivalent of a water well in the scorching desert. We need it. It connects us, informs us, entertains us. But access? Often, it's guarded, locked away behind passwords like a dragon guarding its hoard. This is the reality of our Wi-Fi wilderness. And, frankly, it can be frustrating.
2. The Myth of "Unbreakable" Encryption
Look, let's address the elephant in the room: the illusion of impenetrable security. We've all heard about complex encryption protocols like WPA2 and WPA3. They sound intimidating, right? Like a fortress constructed of digital steel. But, as with any fortress, there are ways in. It's not about “breaking" the encryption in a malicious, hacking-movie sense. It's about understanding how networks function and, in some cases, legally leveraging existing tools.
3. The Secret Laptop Trick: Patience and Persistence
Now, here’s the fun part - the cornerstone of this “secret laptop trick” is all about patience and persistence combined with some clever tools. Think of it like a detective piecing together a puzzle. This "trick" isn't a single magical click of a button, but rather a multifaceted approach. It involves understanding network landscapes, familiarizing yourself with some open-source tools (think of them as your digital Swiss Army Knife), and, of course, a healthy dose of common sense.
4. Your Digital Swiss Army Knife: Essential Tools of the Trade
So, what are these essential tools? Well, we can’t provide specific step-by-step guides. We are not encouraging illegal activity. However, let's gently nudge the door open on the kinds of techniques that are out there. These techniques may involve:
- Network Scanners: These are like digital binoculars, allowing you to "see" the Wi-Fi networks around you, their signal strength, and the channels they're using.
- Packet Analyzers: Imagine a tool that eavesdrops on network conversations. Packet sniffers help you examine the data packets traveling across a network.
- Password Cracking Software: These tools, when used ethically and with permission, can attempt to identify passwords given a valid dataset.
- Wi-Fi Adapters: Some adapters are designed for more advanced network analysis.
(Again, the use of these tools must comply with all ethical and legal requirements)
5. Permission is Paramount: Ethical Considerations
Let's be explicitly clear: We are not advocating for any illegal activities. Accessing a Wi-Fi network without permission is a serious offense. This “trick” is about understanding the possibilities and learning how networks function, not promoting illegal access. Always obtain explicit permission before connecting to any network you don’t own!
6. Understanding the Network Landscape: Your First Step
Before diving into any "tricks," you need to understand the terrain. Take a look at your surroundings. Are you in a densely populated area with many Wi-Fi networks? Are the networks using strong or weak security protocols? Observe, study, and educate yourself. Knowledge is your greatest weapon.
7. The Legal Minefield: Stay on the Right Side of the Law
Navigating the Wi-Fi landscape is like walking through a minefield. One wrong step, and you could find yourself in serious trouble. This information is purely for educational purposes, and the use of these tools should strictly adhere to all applicable laws and regulations.
8. The Open Source Advantage: Power in Your Hands
One of the beauties of the digital world is its open-source community. There are countless free and open-source tools available for network analysis and security testing. They are often user-friendly, powerful, and regularly updated.
9. Cracking Passwords: A Delicate Topic
Let's address the big one: password cracking. It's a complex subject, and we must reiterate the importance of ethical use. Password cracking software utilizes multiple techniques to attempt to find network passwords. This often involves brute-force methods, trying every possible combination, or dictionary attacks, using a list of commonly used passwords.
10. The Art of Social Engineering: Human Weakness
Another aspect, which is less technical and more human - social engineering. Sometimes, the weakest link in any security system isn't the technology, it's the human using it. This is about being observant, being aware, and never taking a chance that might lead to a security breach.
11. Strengthening Your Own Wi-Fi Security: The Defensive Approach
Want to flip the script? Instead of trying to "unlock" someone else's Wi-Fi, focus on securing your own! This involves creating strong passwords, enabling robust encryption (WPA3 is a good start), and regularly updating your router's firmware.
12. Public Wi-Fi Risks: Beware the Shadows
Public Wi-Fi networks, like those in cafes or libraries, are often breeding grounds for security vulnerabilities. Anyone on the network can potentially see your data. Therefore, always use a VPN (Virtual Private Network) when connecting to public Wi-Fi.
13. The VPN Solution: Your Digital Shield
A VPN acts as a secure tunnel, encrypting your internet traffic and masking your IP address. It's like wearing a cloak of invisibility while browsing the web, making it much harder for anyone to intercept your data. Always use a VPN, especially on public Wi-Fi.
14. Beyond the "Trick": Cultivating Digital Awareness
The “secret laptop trick” isn't just about tech; it’s about digital awareness. It’s about understanding how networks work, recognizing potential vulnerabilities, and, most importantly, protecting yourself.
15. The Evolving Landscape: Staying Ahead of the Curve
The digital world is constantly evolving. New threats emerge, and security protocols are updated. Therefore, continuous learning is paramount. Stay informed about the latest security trends, and remember, your digital life is a marathon, not a sprint.
Wrapping Up the Wi-Fi Journey
So, there you have it, a glimpse into the world of Wi-Fi unlock possibilities. Remember, knowledge is power, and understanding the technology empowers you to be a safer, more secure digital citizen. Use this knowledge responsibly, legally, and ethically. Now, go forth and explore the digital frontier, armed with your newfound understanding.
Frequently Asked Questions (FAQs)
1. Is it legal to try and "unlock" Wi-Fi networks?
Absolutely not. Accessing a Wi-Fi network without explicit permission is illegal and can result in serious consequences. The information provided is for educational purposes only.
2. What are the risks of using public Wi-Fi?
Public Wi-Fi networks are often unsecured, making your data vulnerable to interception. Hackers could potentially steal your passwords, credit card information, and other sensitive data.
3. What is a VPN, and why is it important?
A VPN (Virtual Private Network) encrypts your internet traffic and masks your IP address, providing an extra layer of security, especially when using public Wi-Fi. It is important for privacy and security.
4. Are there any “magical” tools that can instantly unlock any Wi-Fi network?
No. There is no magical tool that can instantly unlock any Wi-Fi network. However, certain techniques and tools, when used responsibly, can help you understand network vulnerabilities.
5. How can I secure my own Wi-Fi network?
Use a strong password, enable WPA3 encryption, and regularly update your router’s firmware. Also, consider hiding your network name (SSID) and disabling WPS.
- Principal Keywords: Unlock WiFi Laptop Secret.
- SEO Headline: Unlock WiFi: Secret Laptop Trick!
- Pathway: /Unlock-WiFi-Laptop/
- Meta Summary: Discover a Secret Laptop Trick to unlock any Wi-Fi safely & ethically! Learn about network security, VPNs, and ethical use.
- Image Alt Text: Open laptop displaying Wi-Fi signal, symbolizing the "secret laptop trick" concept.
17DOKUMENTASI Hacking Wifi WPA2 - PSK Menggunakan Bettercap Hashcat education dokumentasi

By XFTExoutic 17DOKUMENTASI Hacking Wifi WPA2 - PSK Menggunakan Bettercap Hashcat education dokumentasi by XFTExoutic

Title: ALAT INI SERIUS BISA MENGETAHUI Password WI-FI BENERAN NGGA SIH
Channel: NanangMrk
ALAT INI SERIUS BISA MENGETAHUI Password WI-FI BENERAN NGGA SIH by NanangMrk
Wifi On Laptop
Unlock ANY WiFi: Secret Laptop Trick Revealed!
Do you ever find yourself yearning for a reliable internet connection, only to be thwarted by locked WiFi networks? The frustration of being digitally disconnected can be immense, particularly when deadlines loom or urgent communication is required. Fear not, for we delve into a clandestine method, a hidden facet of your laptop's capabilities, that grants access to the digital world. We are about to unveil a technique, previously guarded, that promises to shatter the barriers of restricted WiFi, equipping you with the knowledge to connect when you need it most.
The Foundation: Understanding Wireless Networks and Their Vulnerabilities
Before we proceed, it is crucial to understand the fundamental principles underpinning this method. WiFi networks, or Wireless Fidelity networks, operate on radio frequencies, broadcast by a router allowing devices to connect to the internet. These networks are typically secured using various encryption methods, such as WEP, WPA, and WPA2, each offering varying degrees of protection. However, these security measures, while designed to deter unauthorized access, are, in certain circumstances, susceptible to exploitation. We are not going to focus on any illegal activities. Our aim is to equip you with the knowledge of what your device can possibly do and how it interacts with its surroundings.
The Key: Leveraging Your Laptop's Wireless Adapter and Network Configuration
The core of the technique lies in manipulating your laptop's internal components. More precisely, it is about skillfully leveraging your laptop's wireless adapter and its associated network configuration settings. Most modern laptops are equipped with a powerful wireless adapter capable of operating in various modes, including monitoring mode. This special mode allows your laptop to passively "listen" to network traffic without actively participating in the communication. This is the first crucial step.
Step-by-Step Guide: Unveiling the Secret Laptop Trick
Now let us navigate the step-by-step process. Always remember that this information is solely intended for educational purposes. By understanding the capabilities of your equipment, you can secure your network and understand what your equipment can do.
Access the Command Line: Start by opening the command prompt or terminal on your laptop. This will vary slightly depending on your operating system (Windows, macOS, or Linux). For Windows, type "cmd" in the search bar. For macOS, open the "Terminal" application located in the "Utilities" folder within "Applications." For Linux, the terminal can typically be accessed via a system tray icon or through a keyboard shortcut (Ctrl+Alt+T is a common one).
Identify Your Wireless Adapter: You need to identify the name of your wireless adapter. In the command prompt/terminal, type
ipconfig /all(Windows) orifconfig(macOS/Linux) and press Enter. Locate the section that describes your wireless adapter. The name will likely be something like "Wi-Fi," "wlan0," or "en0." Make a note of this name, as you will need it in subsequent steps.Enter Monitor Mode: This is the most critical step. Using the adapter name you just identified, you will activate monitor mode. The commands vary slightly depending on your operating system. For Windows, you might need to use third-party tools. For macOS and Linux, the process is more straightforward.
- macOS: Use the
airportutility. The command will be something like:sudo /System/Library/PrivateFrameworks/Apple80211.framework/Versions/Current/Resources/airport -z. Be prepared to enter your administrator password when prompted. - Linux: Utilize the command:
sudo airmon-ng start <adapter_name>, where<adapter_name>is the name you identified in Step 2. Again, you will likely need your administrator password. - Be sure to check the output of the command to confirm that monitor mode has been successfully enabled.
- macOS: Use the
Scanning for Wireless Networks: With monitor mode enabled on your wireless adapter, your laptop can now gather information about nearby WiFi networks. Use the command
airodump-ng <adapter_name>(Linux) or equivalent tools for Windows and macOS to begin scanning. This command will display a list of all the detected access points, along with crucial details such as their BSSID (MAC address), channel, encryption type, and signal strength.Targeting a Specific Network: From the list of detected networks, select the target network you are hoping to access. Note its BSSID and the channel it is operating on.
Capturing Network Traffic (if applicable and ethically permitted by law): The next step, with caution and full awareness of ethical and legal implications, might involve capturing the network traffic if the target network is vulnerable. This process requires specialized tools often readily available online. This is where the legal and ethical considerations are paramount.
Analyzing Captured Data (where permitted): Once the data has been captured, it can be analyzed to extract useful information, potential passwords, or configurations. Again you are reminded of the potential legal implications.
Ethical Considerations and Legal Boundaries: Navigating the Digital Landscape Responsibly
It is of paramount importance to emphasize the ethical and legal aspects of this technique. Accessing a WiFi network without explicit permission is illegal and can have serious consequences, including fines and legal action. This information is provided for educational purposes only, to understand the complexities of network security. Always respect the privacy and security of others. Using this method to access networks without authorization is strictly prohibited.
Troubleshooting Common Problems and Limitations
This technique is not infallible. Several factors can affect its success, including the strength of the WiFi signal, the type of encryption used by the target network, and the capabilities of your laptop's wireless adapter.
- Signal Strength: A weak signal will make it difficult to capture data or connect to the network.
- Encryption: Modern encryption methods, particularly WPA3, are significantly more secure and more challenging to decrypt.
- Hardware Limitations: Some older or less advanced wireless adapters may lack the necessary features to operate in monitor mode or capture network traffic effectively.
- Operating System Specifics: The commands and tools may vary slightly depending on your operating system.
Beyond Connectivity: Expanding Your Network Security Knowledge
This exploration of network access is not merely about unlocking WiFi. It is about understanding the underlying technologies and vulnerabilities that shape the digital world. By learning about these tools and techniques, you gain a deeper appreciation for the importance of network security principles.
Securing Your Own Network: Implementing Best Practices
Protecting your own WiFi network is just as important as understanding how others work. Here are some critical steps to secure your network:
- Strong Passwords: Use a strong, unique password for your WiFi network. Length and complexity are key. Avoid easily guessable passwords like birthdates or pet names.
- Encryption: Ensure that your router is using the strongest available encryption, usually WPA3.
- Regular Updates: Keep your router's firmware updated. Updates often include security patches to address known vulnerabilities.
- Guest Networks: Consider setting up a guest network for visitors, isolating them from your primary network and sensitive data.
- Network Monitoring: Use network monitoring tools to detect unusual activity or potential security breaches.
Conclusion: Taking Control of Your Digital Connectivity
Unlocking WiFi networks can give you access to the internet. Always remember that this information is provided for educational purposes only. We encourage you to gain a deeper appreciation for digital infrastructure, network security, and the potential vulnerabilities that exist. As you delve into the world of wireless networks, do so with a commitment to ethical and legal conduct.


